Are you thinking about hiring remote team members to help you handle your day-to-day hospitality business tasks?
If so, it’s essential to ensure your information remains safe and secure while they’re working from the other side of the world, no matter where they’re located or what time of day it is.
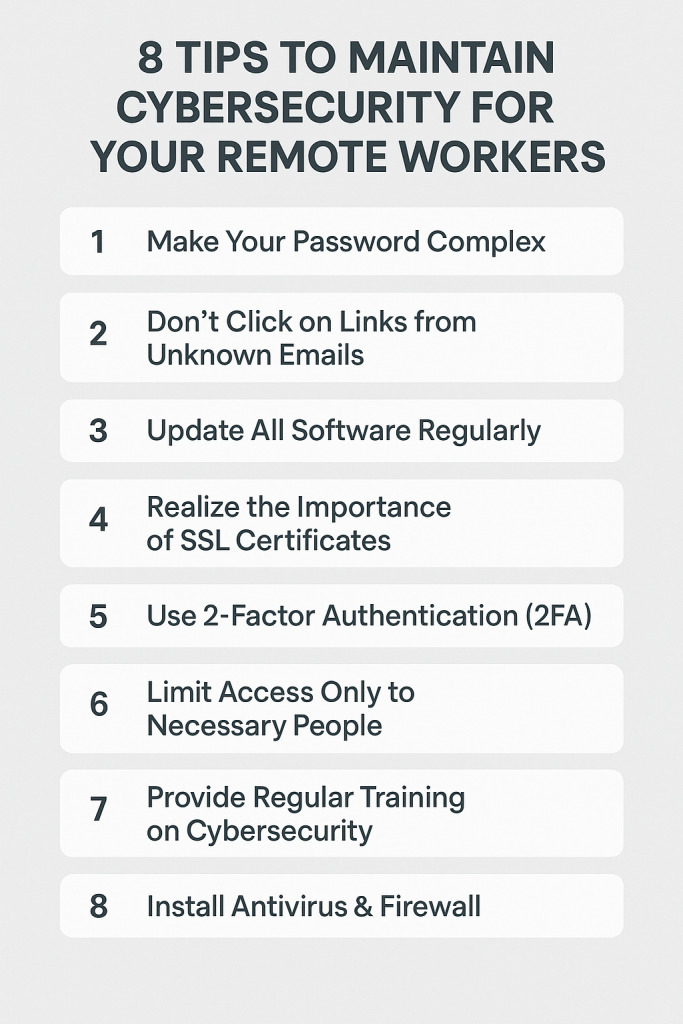
Follow these eight easy tips to protect your network and keep cybercriminals at bay. If you are from the hospitality industry, we have a couple of other articles related to safeguarding hospitality websites from cyber threats and the common cybersecurity threats for hospitality. Please stay with us here for some very useful tips regarding cybersecurity in general for your remote workers.

One careless click can expose sensitive guest data, payment systems or HR documents to the wrong people.
If you are hiring remote workers or already have a hybrid setup, use these 8 practical cybersecurity tips to secure your hospitality business. No jargon. Just real solutions.
1. Strengthen Passwords Using a Password Manager
Use longer passwords with a mix of capital letters, numbers and special characters.
Avoid storing passwords in Excel sheets or notebooks.
Tools like LastPass or 1Password can help:
- Auto-generate complex passwords
- Share credentials securely
- Store passwords for PMS, CRM or OTA portals
Change them every six months or immediately if a device is lost.
2. Never Click Unknown Email Links or Attachments
Phishing is one of the most common cyber-attacks across industries, especially when people are working in isolation.
For your remote hospitality staff:
- Conduct mock phishing tests
- Train them to recognise suspicious email patterns
- Avoid clicking links or attachments without verifying the sender
According to IBM’s 2023 and 2024 report, around 95% of cybersecurity breaches involve human error.
Source: IBM Cost of a Data Breach Report
3. Update Software Every Two Weeks
Do not delay updates. Software updates are not only for performance—they patch vulnerabilities.
Areas to focus on:
- Antivirus
- Operating system
- Payroll and booking software
- Communication tools like Zoom or Slack
Set automatic updates where possible.
4. Use SSL Certificates Across All Your Platforms
If your remote team logs into your internal portal or career page, ensure it uses HTTPS.
SSL certificates help you:
- Encrypt data
- Avoid Google penalties for unsecured domains
- Build trust with candidates, vendors and customers
Even a basic SSL setup improves protection. Many web hosting services offer this at no extra cost.
5. Use Two-Factor Authentication (2FA)
Passwords alone are not enough.
Enable 2FA for:
- Email access
- CRM and booking tools
- Google accounts used for Drive and Docs
Remote workers should use apps like Google Authenticator or Microsoft Authenticator.
Even if a password is leaked, the hacker cannot access the account without the second step.
6. Restrict Access Based on Role
Avoid giving everyone access to everything.
Instead:
- Grant access only to the folders or platforms they need
- Use Google Workspace or Microsoft 365’s access control features
- Keep an audit log to track who accessed what and when
This protects your business if a remote device is compromised.
7. Provide Cybersecurity Training to All Staff
Whether they are a reservations executive or an assistant manager in accounts, your remote employees need training and cybersecurity certifications.
Include:
- How to identify phishing attempts
- Safe Wi-Fi practices
- Proper device usage and reporting suspicious activities
Many reputed platforms like Coursera and Google offer free certification courses.
8. Install Proper Antivirus and Firewall Protection
Do not cut corners here.
Free tools may offer basic scans, but for business use, go with paid antivirus software that covers:
- Real-time protection
- Network security
- File scans for devices that handle guest data or HR records
Ensure it is installed on personal devices if your staff is using them for work.
Final Thought
The hospitality business is based on trust. Your guests trust you with their data, your team trusts your systems, and your clients expect safety in every transaction.
Do not wait for a cyber incident to wake up. Make cybersecurity a habit, not a headache.






